Platform Settings
This page offers answers to common questions about default platform settings, WordPress® settings, and server configuration settings.1 You can use this as a quick reference for many settings and how they are configured or changed.
WordPress Memory Limit
The default WordPress Memory Limit is 40MB for a single site, or 64MB for a Multisite network.
These values can be increased to a maximum of 512MB by inserting the following lines under the “WP Engine Settings” section in your wp-config.php file:
define( 'WP_MEMORY_LIMIT', '512M' );
If you want to define a separate higher or lower memory for the WordPress admin area of the site, can add the following line after the one above:
define( 'WP_MAX_MEMORY_LIMIT', '512M' );
You are free to define whichever memory value works best for your site, as long as it does not exceed 512MB.
To make this edit you’ll need access to the file system of your website. Learn more about connecting to your website with SFTP, or the more advanced SSH gateway.
Maximum File Upload Size
The default maximum upload file size for sites is 50MB (or 1MB for multisite networks). You can check what the site is currently registering for the max file upload size from the /wp-admin/upload.php page:
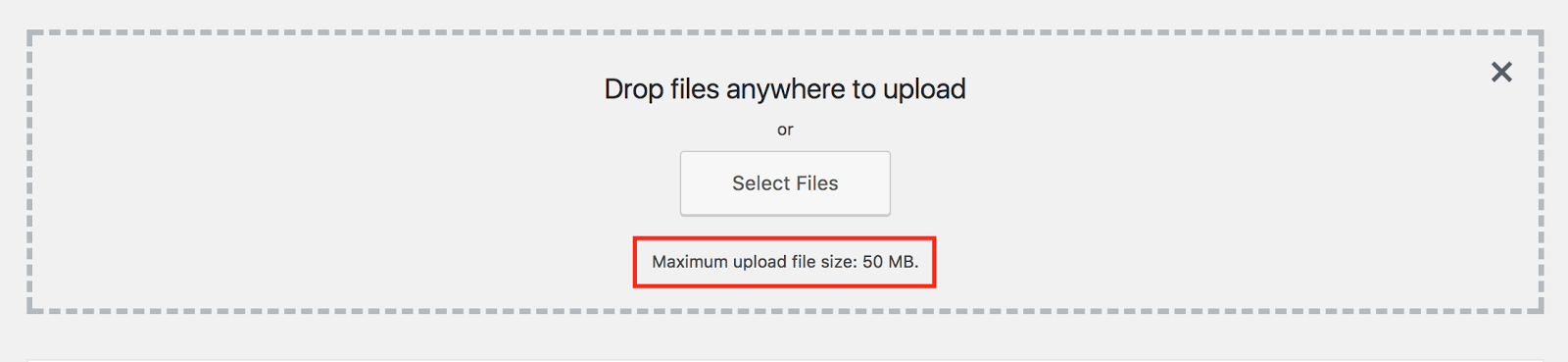
To increase max file upload size up to a maximum of 256MB please contact Support. Any files larger than 256MB must be uploaded via SFTP or SSH Gateway.
Max File Upload Size on Multisite
In addition to reaching out to Support, you will also need to update the network upload size if you are using multisite for WordPress.
- Login to your WordPress admin dashboard
- Click My Sites
- Select Network Admin
- Click Settings
- Locate Max upload file size
- ** The size here is in KB, not MB
If the maximum upload size has been increased but you are still experiencing issues, your website’s Cloudflare account for DNS may be the cause. Max upload for Cloudflare’s Free and Pro plans is 100MB and trying to upload a file larger than this can result in a 413 error in the console from Cloudflare. Try reducing requests below this size into smaller chunks, upload the full resource after disabling Cloudflare’s proxy, or upgrade your Cloudflare account.
PHP Image Resize Limit
WP Engine limits the size of images that can resized using PHP. This size limit is 8000px by 8000px, or 40MP. We’ve put this limit in place to protect server memory and stability, and therefore it cannot be increased.
Plugins that resize images using PHP, such as Smush or ImageMagick, may run into errors if the image is too large. For example you may see the error, width or height exceeds limit. If you are seeing such an error, resize the image below the limitations prior to attempting the upload again.
PHP Execution Restricted
WP Engine servers block the execution of .php files from within the wp-content/uploads/ directory. This directory is intended only for media, it is best practice to not execute PHP from these folders.
Long Query Governor
WP Engine has a governor in place for your benefit to prevent database queries that are extremely long in character length from running and affecting site and server performance. The governor can be disabled with the following define in your wp-config.php file but we advise against it in most cases to prevent performance issues. Optimizing queries so that they no longer receive a KILLED QUERY error is preferable to allowing long queries.
define( 'WPE_GOVERNOR', false );Read more about the governor and long query errors in the Error Logs and Common Errors article.
Post Revisions
WordPress Post Revisions, or autosaves, store a record of each saved draft or published update for a post. This system allows a user to see the last few changes and to restore a page or post to a previous version. While great in theory, revisions cause the database to grow exponentially and a large database can directly impact site performance.
Every WP Engine site has WordPress revisions disabled by default. If you need a more extensive revision management system, we recommend using a third-party editing system rather than relying on WordPress revisions.
Revisions can only be enabled by contacting Support. Revisions cannot be enabled in the wp-config.php or php.ini files, as this will be overwritten at the server level.
Enable revisions before importing. If you are importing a site with revisions and you want to keep the revisions, you must contact support to enable revisions before importing the site. Otherwise revisions will get cleaned up by our DB cleanup script if they are not enabled.
If you migrated a site with existing revisions that you would like to preserve, reach out to Support to have revisions enabled.
- Support can help you enable 3 revisions for your posts to start. Revisions should not exceed 5.
- Old revisions will be automatically removed after 60 days.
NOTE
Enabling revisions is not a retroactive change. Only revisions generated after the feature has been enabled will be stored moving forward.
If you would like to clean up your database and delete any existing database revisions, the following query can be run from phpMyAdmin.
DELETE FROM wp_posts WHERE post_type = “revision”;
Sending Email
WP Engine allows general WordPress emails such as password resets to be sent through WordPress below a certain reasonable quantity. However, for sending a large number of emails, such as a newsletter or email blast, we impose a limit and require the use of an email API or an SMTP plugin.
As Port 25 is blocked for all services, we highly recommend using an email service that sends email via API, or an alternative port (such as port 2525).
More information about WP Engine’s email policy can be found here.
TLS Version
All WP Engine servers have TLS 1.2 and 1.3 enabled by default.
TLS 1.0 and 1.1 have been deprecated on WP Engine. As TLS 1.0/1.1 deprecation happened across the industry, and we do not offer the option for customers to defer or opt into a version lower than TLS 1.2. For a majority of customers, usage of TLS 1.2+ should not cause any noticeable impact.
Check out our guide for more information about TLS and SSL.
GZIP and Brotli Compression
WP Engine automatically uses GZIP or Brotli compression to optimize performance of static files (like images, text files, JavaScript, and CSS) on your web server. As a result, GZIP and Brotli directives should not need to be added separately.
If the browser requesting the file supports Brotli compression, the file will be served compressed with Brotli. If the requesting browser does not support Brotli the file will be served compressed with GZIP.
The following file types are automatically compressed by WP Engine with Brotli:
text/plain
text/css
application/javascript
application/x-javascript
text/xml
application/x-font-opentype
application/x-font-truetype
application/x-font-ttf
application/xml
application/xml+rss
font/eot
font/opentype
text/javascript
image/x-icon
image/bmp
image/svg+xml
The following file types are automatically compressed by WP Engine with GZIP:
application/rss+xml application/vnd.ms-fontobject application/wasm application/x-javascript application/x-web-app-manifest+json application/xhtml+xml application/xml application/xml+rss font/otf image/bmp image/svg+xml image/x-icon text/cache-manifest text/calendar text/css text/javascript text/log text/markdown text/plain text/richtext text/vcard text/vnd.rim.location.xloc text/vtt text/x-component text/x-cross-domain-policy text/xml text/xsd text/xsl
Max Execution Time
Default max_execution_time for scripts is set to 60 seconds.
This setting can only be decreased, and cannot be increased. If you are performing a task which will take over 60 seconds to complete, the task should be broken into smaller segments and run in batches.
Max Input Vars
The default max_input_vars setting is 10000, indicating no more than 10,000 variables can be attached to any request.
This setting cannot be adjusted, as this is set at a platform level and higher values will have negative performance implications.
NOTE
WP Engine does not support .htaccess. Review our guide for alternatives.
LOAD DATA MySQL Function
The LOAD DATA statement in MySQL is disabled on the WP Engine platform for security reasons. Some potential alternatives to using the LOAD DATA function are:
- Using INSERT statements in MySQL
- Using the graphical phpMyAdmin editor from the WP Engine User Portal to import data
- Using an SSH connection to import data with WP-CLI or a database tool like MySQL Workbench
Security Headers
If you want to ensure extra security on your site through the use of headers, many are already added by default. If the header you’d like is not enabled automatically, they can be added through the Web Rules page in your User Portal.
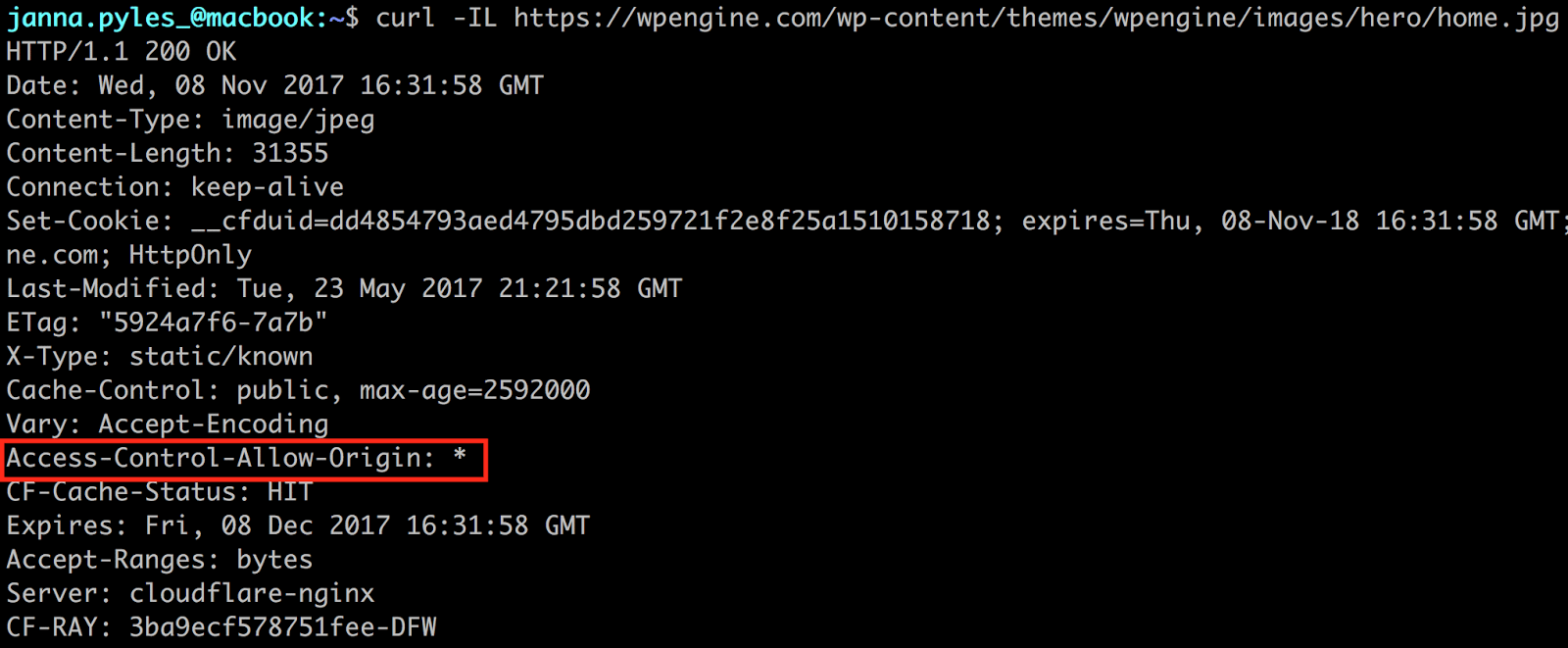
CORS
Cross-Origin Resource Sharing headers are defined by default for all static resources on sites (images, styles, JavaScript, etc). You can see this by curling for the headers on a static file. For example:
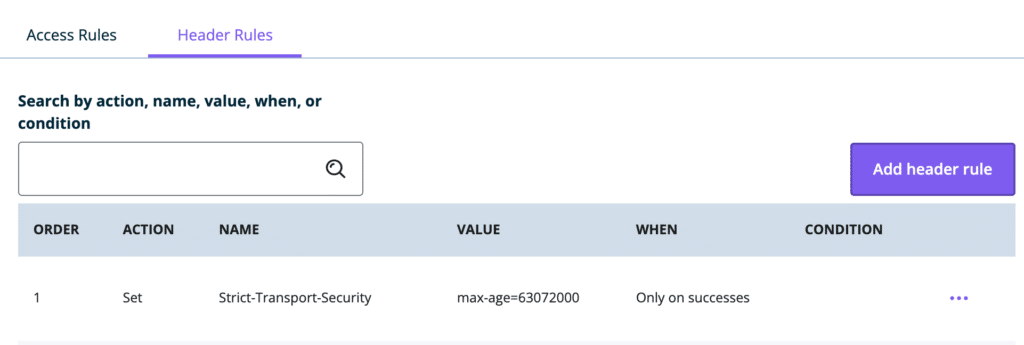
HSTS
HTTP Strict Transport Security (HSTS) is a security policy allowing web servers to declare that browsers (or other complying user agents) should only interact using secure HTTPS connections. Setting this up on WP Engine can be done by adding a header to the Web Rules area of the User Portal.
This rule is the simplest HSTS header that can be added, indicating that once a browser has read the header it should remember it for 63072000 seconds (2 years).
add_header Strict-Transport-Security "max-age=63072000";When added as a header rule it will look like the following:
Optional directives:
HSTS headers come with two additional directives: preload and includeSubdomains. Adding both of these additional directives would look like this:
add_header Strict-Transport-Security "max-age=63072000; includeSubDomains; preload";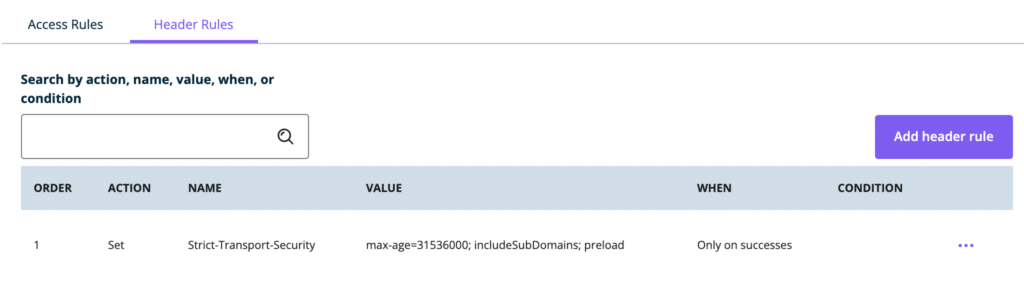
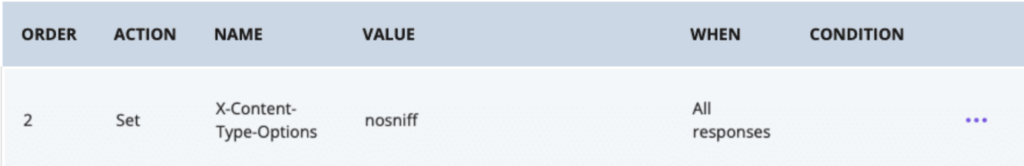
Below are all the default directives you will typically need to pass a security header test. These headers can be modified as-needed.
- Action: Set
- Name:
X-Frame-Options - Value:
SAMEORIGIN - When: All responses
- Conditions: None are needed

- Action: Set
- Name:
X-Content-Type-Options - Value:
nosniff - When: All responses
- Conditions: None are needed
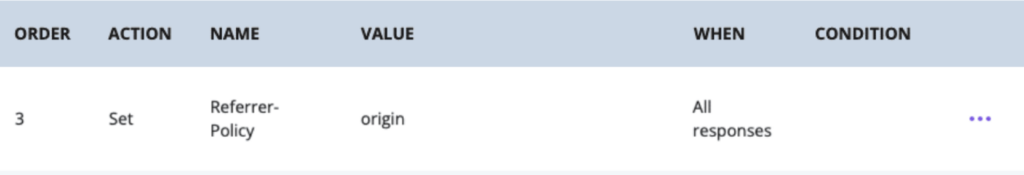
- Action: Set
- Name:
Referrer-Policy - Value:
origin - When: All responses
- Conditions: None are needed
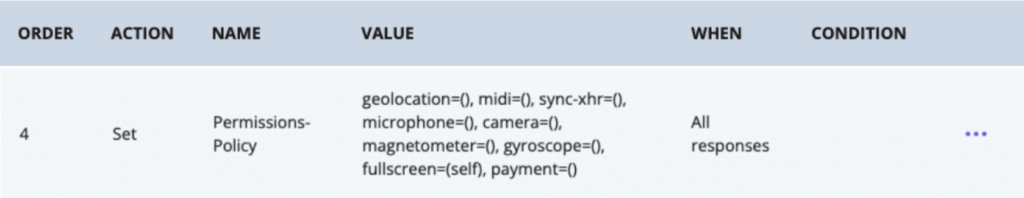
- Action: Set
- Name:
Permissions-Policy - Value:
geolocation=(), midi=(), sync-xhr=(), microphone=(),camera=(), magnetometer=(), gyroscope=(), fullscreen=(self), payment=() - When: All responses
- Conditions: None are needed
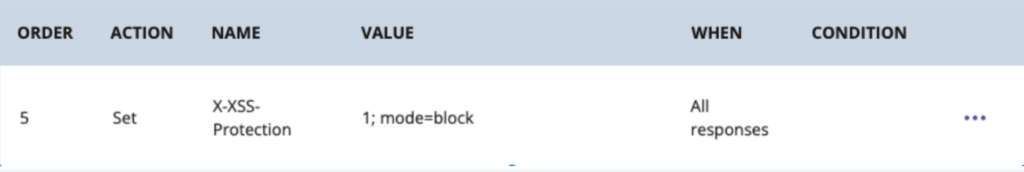
- Action: Set
- Name:
X-XSS-Protection - Value:
1; mode=block - When: All responses
- Conditions: None are needed
A few notes about the directives:
- The
includeSubdomainsaffects all subdomains, even ones on other hosts. This is due to the browser registering the HSTS header with the directive and will apply it to all relevant subdomains - The
preloaddirective allows a site to be to be registered at https://hstspreload.org/, which adds the domain to the Chrome HSTS preload list that is hard coded in to browsers. Other browsers also use this list.- If there is an error with the verification on this service, make sure that no domain-level redirects are set in the User Portal. For example, non-www to www or vice versa. Any redirects from the root domain must be removed completely.
- Removal from the
preloadlist can be a lengthy process:Be aware that inclusion in the preload list cannot easily be undone. Domains can be removed, but it takes months for a change to reach users with a Chrome update and we cannot make guarantees about other browsers.
Misc Security Headers
The following security headers can also be added through the Web Rules page of the User Portal. We’ve included examples of the most common header options, but many can be modified to suit your specific needs.
Vary
Ensures the correct content is delivered for the specific browser. This is particularly relevant when caching or proxy layers are at play, as older browsers may not understand more modern compression or file types. The following is the recommended rule configuration.
proxy_set_header Vary "Accept-Encoding";X-XSS Protection
Protects (typically older) browsers from cross-site scripting attacks. The following is the recommended configuration rule.
add_header X-XSS-Protection "1; mode=block";Feature Policy
Allows opt-in and opt-out standardization for features on a website, particularly when APIs or third-party apps are used. The following is a usable example but it can be modified if necessary.
add_header Feature-Policy "geolocation 'none';midi 'none';notifications 'none';push 'none';sync-xhr 'none';microphone 'none';camera 'none';magnetometer 'none';gyroscope 'none';speaker 'self';vibrate 'none';fullscreen 'self';payment 'none';";Referrer-Policy
Identifies the address of the webpage associated with a requested resource. The following is a usable example but can be modified for different needs.
add_header Referrer-Policy "origin" always;X-Content-Type-Options
Allows deliberate setting of MIME types by forcing requests to follow and not change the set content-type. Learn more about this header on Mozilla.
add_header X-Content-Type-Options "nosniff" always;X-Frame-Options
Determines whether or not a page can be loaded as a <frame>, <iframe>, <embed> or <object>. The following tells the page that it can only be displayed as one of these types on a page with the same origin. This rule can be modified to allow other URIs if needed.
add_header X-Frame-Options "SAMEORIGIN" always;Server Modules
WP Engine has a specific set of platform-wide server modules which cannot be modified, removed, or added. To see a full list of modules, versions, and default settings, you can create a PHP Info file.
Disabled Functions and Modules
Our system administrators have already pre-configured server settings to best suit the needs of the majority of our clients. Some functions cannot be modified from site to site or in the php.ini file as they are configured at a server level.
Here are some functions that have been disabled and therefore are not able to be altered:
- apache_child_terminate
- apache_get_modules
- apache_get_version
- apache_getenv
- apache_note
- apache_setenv
- disk_free_space
- disk_total_space
- diskfreespace
- dl
- exec
- passthru
- pclose
- pcntl_exec
- popen
- posix_getpwuid
- posix_kill
- posix_mkfifo
- posix_setpgid
- posix_setsid
- posix_setuid
- posix_uname
- proc_close
- proc_get_status
- proc_nice
- proc_open
- proc_terminate
- shell_exec
- show_source
- system
- opcache_get_configuration
- opcache_get_status
- auto_prepend_file
Miscellaneous Modules
| Module | Is it installed? |
|---|---|
| ionCube Loader | No |
| cURL support | Yes |
| SOAP client | Yes |
| Imagick | Yes |
Environment Variables
- WP Engine does not currently have a feature for environment variables on our WordPress (PHP) servers.
- WP Engine does currently have a feature for environment variables on our Headless Platform (Node.js) servers.
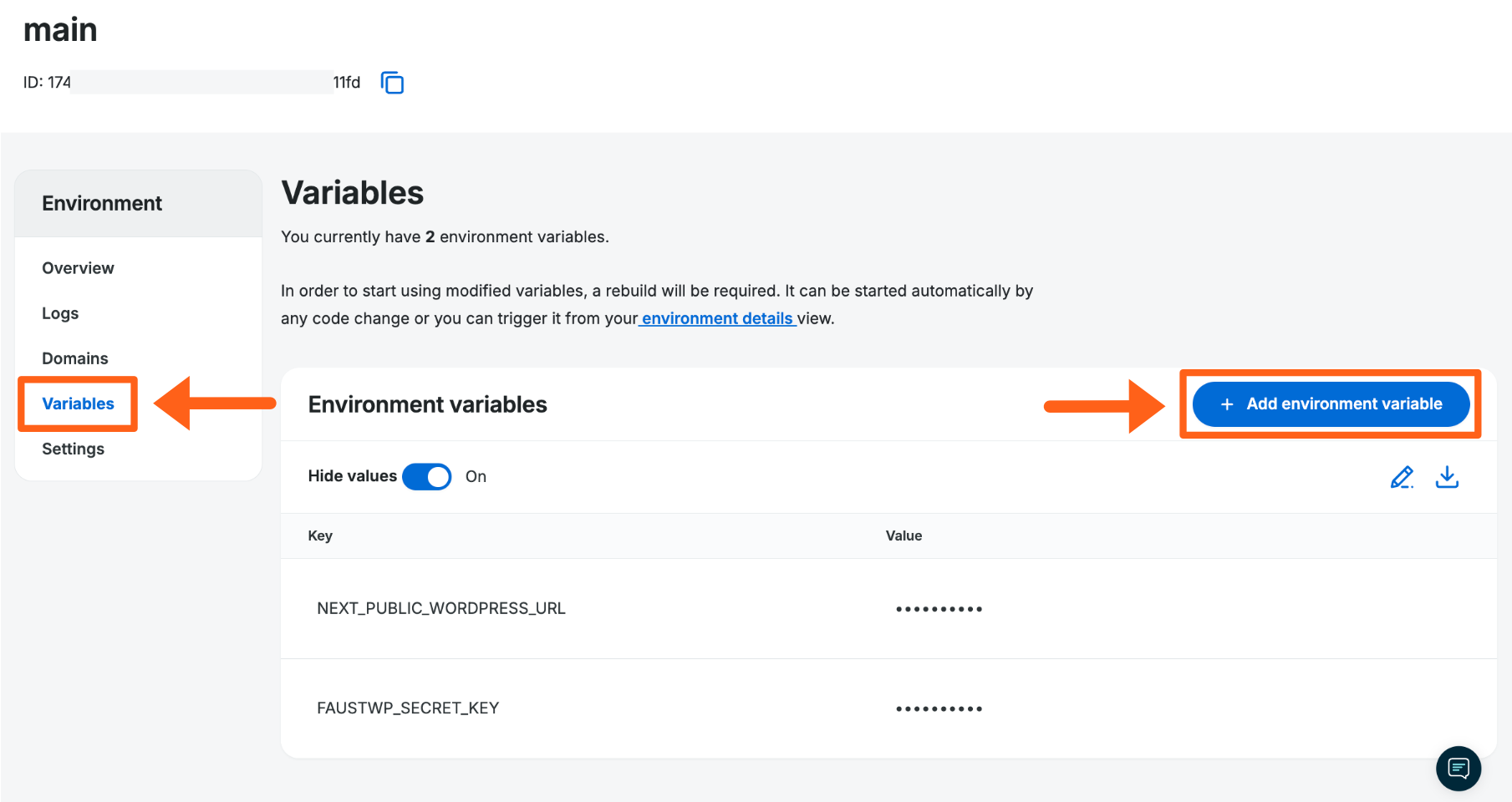
- Environment variables are also referenced in relation to CI/CD pipelines where you would push changes to WP Engine from a 3rd-party repository like Github or Bitbucket, etc. In these cases you would be adding an SSH key as an environment variable inside of those 3rd-party apps so they can connect to WP Engine.
Disallowed Plugins
Most plugins are allowed on the WP Engine platform, however a handful of plugins we specifically disallow, as they will cause issues with either security or performance.
View our current list of disallowed plugins.
Although they are not disallowed, some plugins are still incompatible with the WP Engine platform. This is most impactful for plugins and themes utilizing ionCube. The ionCube Loader module is not available on WP Engine due to the significant performance issues it causes.
Learn more about unsupported modules.
PHP Version
PHP Versions are regularly released and deprecated. To see which versions are currently available on the WP Engine farm and how to change versions, check out our PHP Upgrade Guide.
MySQL Version
WP Engine uses MySQL 8.
Learn more about MySQL 8 compatibility and how to find a site’s current MySQL version here.
Configuration Files
There are several site and server-wide configuration files in place for each environment. Some files are accessible and able to be modified, while others are not.
| Configuration file | Is it editable? |
|---|---|
| php.ini file | No. Server-wide PHP settings are unable to be changed. |
| .htaccess file | No. WP Engine has deprecated the .htaccess file. |
| wp-config.php file | Yes. This file can be edited, but there are many WP Engine-specific settings in this file which should not be changed. For the best results, put custom entries in the “WP Engine Settings” section at the bottom. |
| nginx.conf file | No. Server or site-specific Nginx settings are not able to be adjusted. If there is a specific Nginx setting you wish to adjust, please contact Support to see if there are any internal changes which may be made |
WP Engine MU Plugins
There are certain must-use plugins that you may see added to your WordPress website by WP Engine. These are added for specific reasons, such as security or functionality.
While we don’t recommend it, some of these plugins can be disabled. If you’d like to remove a WP Engine MU plugin, reach out to our Support team.
WP Engine Common
The wpengine-common plugin provides most of the WP Engine platform functionality. Platform features provided by this plugin can be seen in your wp-admin dashboard under the WP Engine menu icon.
The name of the plugin in your wp-content/mu-plugins folder is mu-plugin.php which references files in the wp-content/mu-plugins/wpengine-common folder. The name of the plugin in your WordPress dashboard is WP Engine System. You can find this listed under the Must-Use tab of the plugins page.
This plugin provides access to platform functionality, such as post-processing and cache adjustments. It can be accessed at /admin.php?page=wpengine-common
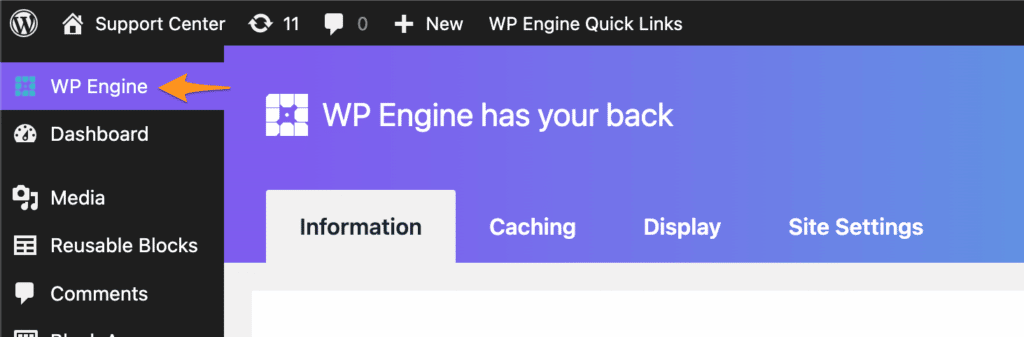
This plugin cannot be disabled, however the menu icon can be hidden with custom coding.
Hiding Log Links
In addition to hiding the sidebar menu item with custom code you may also want to hide the error log links. The WP Engine menu page shown in the screenshot above has a button to download Current error logs. The link shown when you hover on the button pictured below has a visible api key which you may want to hide in certain cases. The same link to the error logs also appears in the WP Engine Quick Links in the top admin bar.
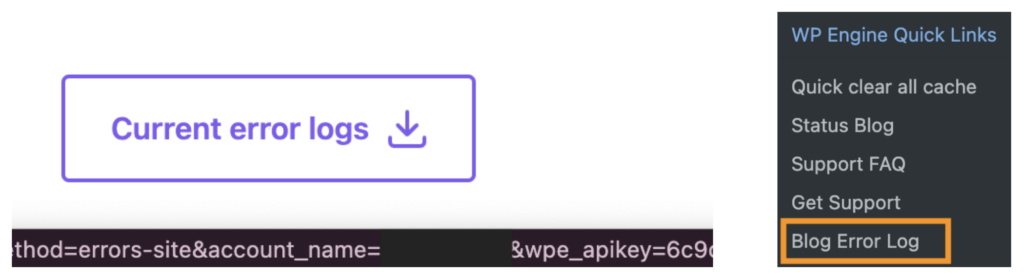
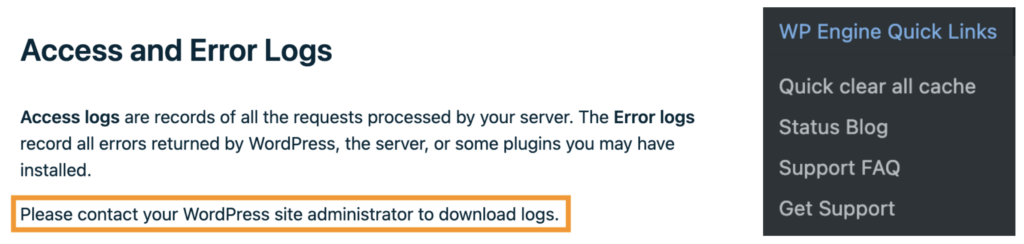
One example of when you may want to hide them would be if you have a multisite website where you only want the links to be visible to Super Admins. For this reason, our team has created a filter that you or your developer can use in your theme’s functions.php file to hide the links. The filter name is wpe_should_render_log_links.
If you or your developer use the filter to hide them, the buttons will be replaced with a message and the Quick Link menu item will be gone as shown in the screenshots below.
Below are some code examples of using the filter:
// example to only show links to Super Admins in multisite
add_filter( 'wpe_should_render_log_links', 'should_render_log_links' );
function should_render_log_links( $render ): bool {
if ( is_multisite() && ! current_user_can( 'manage_network_options' ) ) {
return false;
}
return $render;
}// example to only show links to admins with an additional custom capability created and named view_log_links
add_filter( 'wpe_should_render_log_links', 'should_render_log_links' );
function should_render_log_links( $render ): bool {
if ( ! current_user_can( 'administrator' ) || ! current_user_can( 'view_log_links' ) ) {
return false;
}
return $render;
}Make sure you thoroughly test your code before implementing the filter on a production environment.
WP Engine Quick Links Menu
As part of the WP Engine plugin, a toolbar can be found in the wp-admin header bar of your site. This toolbar, called WP Engine Quick Links, appears as shown below when you are logged in.
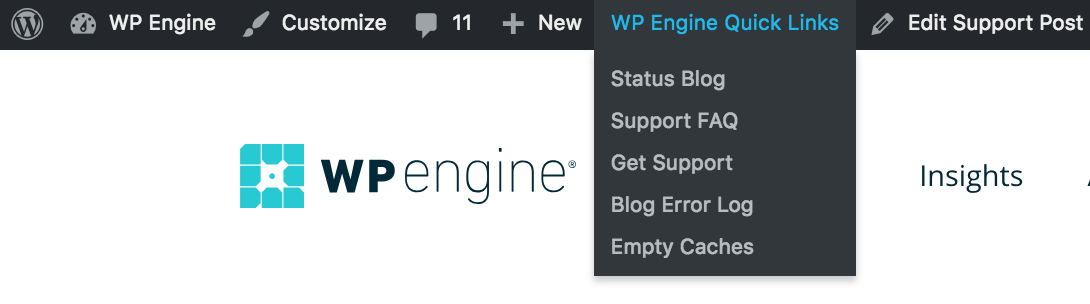
While some people may want to this toolbar to display, others may choose to have it disabled, or only display for users of a specific role.
The Quick Actions menu can be enabled/disabled for all users (excluding Administrator), or enabled/disabled for specific roles.
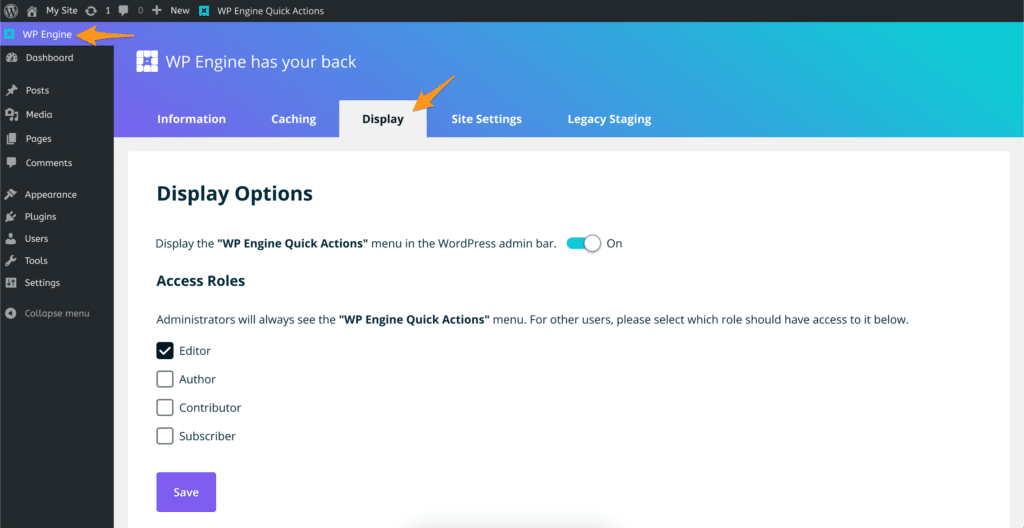
- Login to your WordPress dashboard (wp-admin)
- Click on the WP Engine tab in the main menu to open our plugin
- Select Display
- Toggle WP Engine Quick Actions Off to hide the menu completely, OR select certain roles to grant menu access
- Click Save
WP Engine Seamless Login
The wpe-wp-sign-on-plugin plugin files are added for the WP Engine “Seamless Login” feature. This feature gives you the ability to securely log in to the wp-admin of a website directly from the User Portal.
To learn more about this functionality see the Seamless Login guide.
WP Engine Security Auditor
The wpengine-security-auditor plugin performs two main functions:
- Log security-relevant events to the Site Error Log. Examples of logged events are login, role changes, and plugin upgrades.
- Periodically calculate and log checksums for plugins, themes, and WP core files.
For a full list of these items as they display in your logs, see our guide.
We do not recommend disabling this plugin as it adds security features. However, if you find too many events are being logged it can be disabled by adding the following feature flag to your wp-config.php file:
define('WPENGINE_SECURITY_AUDITOR_ENABLED', false);Force Strong Passwords
The plugin force-strong-passwords is added to force all users with access to the wp-admin are of your site to use strong passwords. Strong passwords are only required for Administrator, Editor, and Author roles. It is not required for “weaker” roles like Subscriber and Contributor. Our system to force a strong password only requires users to set a strong password when resetting the password from the wp-login.php page.
This plugin should never be disabled as it can create a serious security vulnerability in your website.
To learn more about forcing strong passwords, see our full guide.
Hidden Site Settings
There are some hidden settings that you will not be able to change on your own website. WP Engine closely manages certain settings in order to protect server performance or for security purposes. Contact Support to request modifications to the following settings.
- Maximum File Upload Size
- Defaults:
- Single site: 50 MB
- Multisite: 1 MB
- Max: 256 MB
- To update a Multisite website you must also change the value in Network Admin > Settings (/wp-admin/network/settings.php).
- Defaults:
- Post Revisions
- Default: 0
- Max: 5
- Enabling post revisions is not retroactive.
- Login Protection
- Our protection against login attacks can be turned off if you have a custom login form or page that is getting blocked by it, but this is not recommended.
- This is most often the root cause of instant 502 errors when logging in to a website using custom login functionality.
- Read Only Mode
- You can ask a Support agent to turn on Read Only Mode which will disable the site’s ability to write to PHP files and to use the Theme and Plugin editors, etc.
- SFTP and SSH Gateway can still be used to modify these files.
- Regenerate Database Password
- Support agents can run a command that generates new database credentials in your wp-config.php file.
- This is a common solution when receiving the error “error establishing a database connection”.
- Cache Exclusions
- Support agents can add an exclusion rule that causes html to not be cached for a specific page that matches one of three types of conditions:
- Page URL path
- A cookie present on the page
- A query string argument present in the page URL
- Items cannot be excluded from object caching.
- Support agents can add an exclusion rule that causes html to not be cached for a specific page that matches one of three types of conditions:
- Nginx Rules
- If you need a rule added for Nginx, first try to see if it’s something that you can add in the User Portal with Web Rules. If you need additional custom Nginx rules, ask Support to try to paste the custom rule into your website’s settings. Not all types of rules can be added (e.g. server directives, etc). Additionally Support cannot assist with writing custom Nginx rules.
- Reset WordPress Core Files
- Support can reinstall your website’s default WordPress core files if they have been modified and are causing an issue with plugins or themes on your site.
- Reset Site To Default
- Support can reset an environment back to a blank default WordPress site. This will remove all content and database entries.
NEXT STEP: Learn more about .htaccess alternatives
